Essentially, double-spending is the concept that someone can replicate Bitcoin or cryptocurrency transactions with funds being sent to two different addresses simultaneously.
So, why is double-spending such a problem? And how can it be prevented in a blockchain?
Understanding the Blockchain
The blockchain which undergirds a digital currency like bitcoin is not able to prevent double-spending on its own. Rather, all of the different transactions involving the relevant cryptocurrency are posted to the blockchain, where they are separately verified and protected by a confirmation process. In the case of bitcoin and many other cryptocurrencies, transactions that have been confirmed in this way become irreversible; they are posted publicly and maintained in perpetuity.
Bitcoin was the first major digital currency to solve the issue of double spending. It did so by implementing this confirmation mechanism and maintaining a common, universal ledger system. In this way, the bitcoin blockchain retains records of time-stamped transactions going back to the founding of the cryptocurrency in 2009.
In Bitcoin terms, a "block" is a file of permanently recorded data. All recent transactions are written into blocks, much like a stock transaction ledger on an exchange. Information from blocks is added to the ledger every few minutes; all nodes on the network maintain a copy of the blockchain ledger. Users are able to navigate the blockchain for bitcoin and review transactions in terms of quantity only. Details about the identities of the buyer and seller in any transaction are protected by high-level encryption, which also protects the ledger from tampering by outside sources. When the blockchain ledger is updated, so too are all bitcoin wallets.
What is Double-Spending?
With regard to digital currency, guaranteeing that a particular unit cannot be duplicated is extremely important. This is because digital information can be relatively easily reproduced by tech-savvy individuals familiar with the blockchain network, and computing commands required to tamper with it.
As we’ve already established, double-spending is essentially where the same funds are sent to two recipients simultaneously.
It occurs when a blockchain network is disturbed, and the cryptocurrency is basically stolen. The person responsible would then send a copy of the transaction to make it look genuine, or even delete the transaction altogether to make it look like it had never occurred.
Without proper countermeasures to resolve such an issue, the entire transaction will be rendered fundamentally destabilized and undermined. Users have no protocol to verify whether the funds they have received aren’t also being spent elsewhere.
Hence, for a digital currency to function reliably, there have to be strict mechanisms preventing this kind of behavior.
How Does Double-Spending Work?
Double-spending destroys and compromises the technological basis of a blockchain. Its whole concept is the opposite of what the blockchain is all about. Hence, the possibility of double-spending would ultimately undermine the trust in a cryptocurrency such as Bitcoin or any other blockchain-based digital currency.
A commonly used analogy for this conundrum is known as the Byzantine Generals’ Problem. This highlights the challenge numerous parties have to face when they do not trust each other and have to participate in a joint venture where they require cooperation to succeed. This analogy explains the issue of disagreement in a decentralized system.
In this analogy, when all generals lead a coordinated attack with their armies, they will achieve victory. However, as soon as a general defects or attacks another general, the entire battle, similar to a blockchain, will be compromised and eventually lost.
As a result, cryptocurrencies must deploy Byzantine Fault Tolerance (BFT) into their protocols. This protocol implies that a computer system must keep functioning up to a satisfactory level despite errors, breakdowns, orparticipants behaving contrary to the designated plans or cheating the system.
Examples of Double-Spending
Now that we’ve understood the basis of double-spending, let’s look at three popular ways scammers perform a double spend.
1. 51% Attacks (Majority Attack)
A 51% attack on a blockchain network occurs when a sole individual or organization controls most of the hash rate, causing potential network disruption. When this happens, the so-called “attacker” attains enough mining power to omit or alter the sequence in which transactions are conducted purposely.
During a 51% attack, the attacker could reverse transactions made by them during this time, leading to a double-spending problem. Moreover, the attacker can also inhibit some or all transactions from confirmation (i.e., a transaction denial of service) and prevent some or all other miners from mining, something known as “mining monopoly.”
Bitcoin Gold, a cryptocurrency that came about as a fork of Bitcoin, was a victim of such attacks in 2018 and 2020.
2. Race Attacks
A race attack involves sending two opposing transactions simultaneously with similar funds; however, only one transaction is confirmed.
During such an attack, the main idea is to invalidate other payments by validating only that transaction that benefits the attacker, i.e., funds sent to an address that they can control.
Also, race attacks need recipients who accept unconfirmed transactions as a form of payment.
3. Finney Attacks
Unlike a race attack, a Finney attack involves the attacker pre-mining a single transaction into a block; however, it is not broadcast immediately to the entire network.
In this kind of double-spending attack, the attacker spends the same coins in a different transaction and then broadcasts the previously mined block, thus invalidating the payment.
These attacks need to occur in a distinct sequence. Likeike race attacks, they also depend on the recipient accepting unconfirmed transactions.
How Bitcoin handles the Double Spending Problem?
Bitcoin handles the double-spending problem by implementing a confirmation mechanism and maintaining a universal ledger called blockchain.
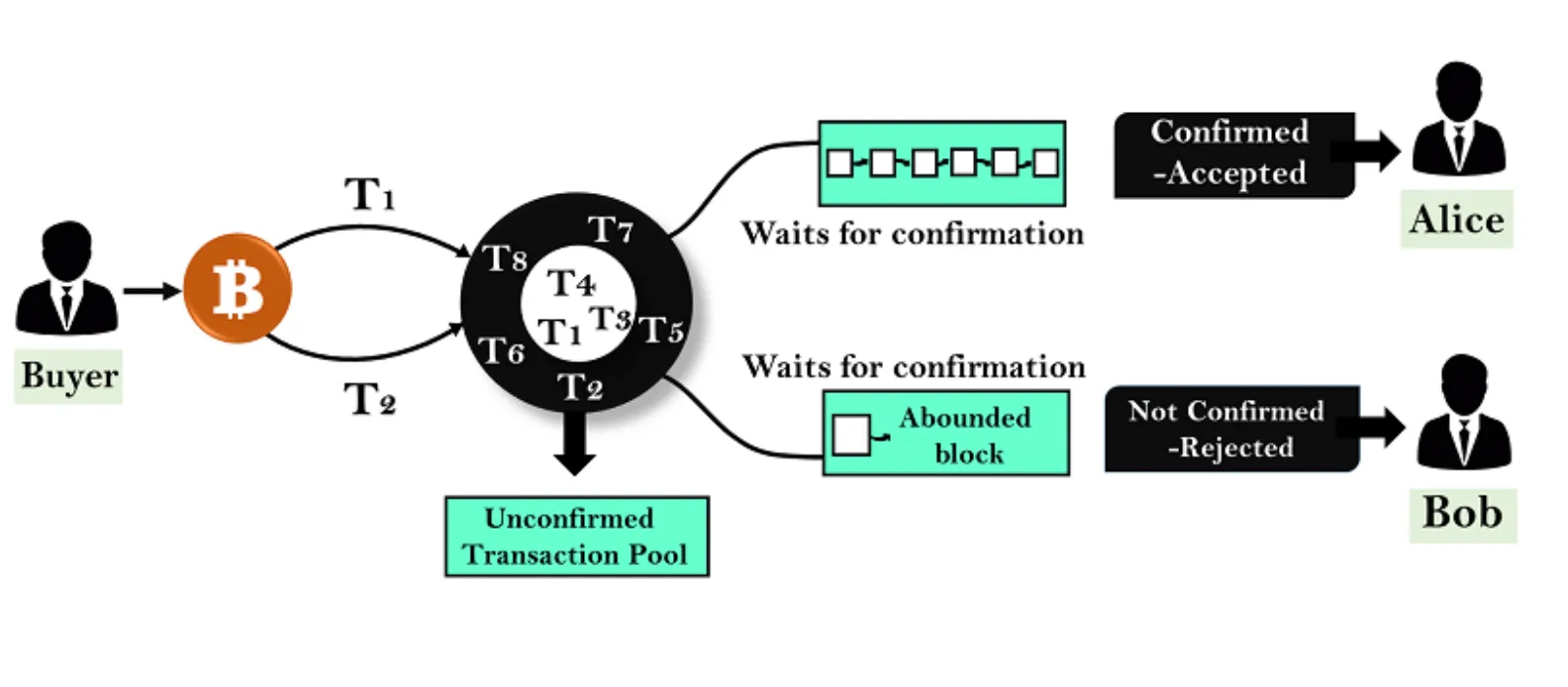
Let us suppose you have 1 BTC and try to spend it twice. You made the 1 BTC transaction to Alice. Again, you sign and send the same 1 BTC transaction to Bob. Both transactions go into the pool of unconfirmed transactions where many unconfirmed transactions are stored already. The unconfirmed transactions are transactions which do not pick by anyone. Now, whichever transaction first got confirmations and was verified by miners, will be valid. Another transaction which could not get enough confirmations will be pulled out from the network. In this example, transaction T1 is valid, and Alice will receive the bitcoin.
How to Combat Double-Spending?
Preventing double-spending involves a more strenuous verification process and ensures that the same input cannot be shared over multiple transactions. There are two primary ways to combat double-spending:
1. Centralized Clearing Counterparty
Centralization can potentially mitigate the inherent risk of double-spending in transacting digital currency. It is done by implementing a central and trusted third party to verify the transactions. The added entity would perform a function equivalent to central counterparty clearing.
In finance, central counterparties are often financial institutions that take on counterparty credit risk between two parties and ensure that a transaction clears. The services are commonly applied to facilitate the trading of financial derivative instruments.
2. Blockchain
Decentralized digital currencies, such as Bitcoin, utilize consensus mechanisms that verify transactions with certainty. The consensus mechanisms are alternatively known as proof-to-work. Practically, the mechanism ensures that each participant node verifies the transaction. Therefore, Bitcoin comes with a historical public ledger facilitated through blockchain that provides empirical verification of property rights and transfer.
In order for a market participant to fraudulently double spend, they will need to use a significant amount of computing power to eliminate the previous blocks in the chain, and effectively double-spend the transaction. Additionally, as time passes, confirmations of the block exponentially grow, further protecting the integrity of the transaction.
How a Successful Double-Spending Attack is Administered
- Broadcast to the network a transaction where attacked merchant receives payment
- Secretly mine a branch that is built upon the block before the transaction, a transaction that pays the attacker
- Once the transaction to the merchant receives enough confirmations, and the merchant sends the product
- Continue the secret contradictory brand until it is longer than the public transaction, and then make the blocks public. The network will identify the secret branch to be valid because it is longer than the public block, and the payment to the merchant will be replaced by the payment to the attacker.
How Likely Are Double-Spending Attacks to Occur?
Even though it has occurred, thankfully double-spending in a blockchain is difficult to achieve.
This is because once a cryptocurrency’s blockchain becomes large enough, as with the case of Bitcoin or Ethereum, the probability of a single individual or group gaining enough computing power to overthrow all other participants speedily becomes very low.
Moreover, modifying all previously confirmed blocks becomes more problematic as the chain grows, since the blocks are all linked via cryptographic proofs. As a result, the more confirmations in a block, the higher the cost of altering or reversing transactions.
Hence, a successful double-spend attack would perhaps only modify a few recent blocks’ transactions, and only for a relatively short time.
As for Bitcoin, its consensus algorithm, also known as Proof of Work (PoW), ensures that miners can only validate a new block of transactions given all network nodes mutually agree that the block hash given by the miner is correct. The block hash verifies that the miner has put in enough effort, found an effective solution for the block’s problem, and will therefore reward some Bitcoins for solving it.
The Bottom Line
Double spending of Bitcoin is a concern, since it’s a digital currency with no central authority to verify its spending records. This leaves some to question the network’s security and legitimacy of Bitcoin’s network, validators, and monetary supply. However, the network’s distributed ledger of transactions, the blockchain, autonomously records and verifies each transaction’s authenticity and prevents double counting.
Though the blockchain can’t solely prevent double-spending, it is a line of self-defense before an army of decentralized validator nodes solve complex mathematical problems to confirm and verify new transactions are not double spent before they’re permanently added to the network’s permanent ledger.
Cryptocurrencies like Bitcoin can be volatile investments and prices change quickly due to news flow and other factors. Yet it’s that potential for highly fluctuating price changes that compels some investors—particularly those with a long-term investment horizon—to see out crypto as an investment.
🔺DISCLAIMER: The Information in the post isn’t financial advice, is intended FOR GENERAL INFORMATION PURPOSES ONLY. Trading Cryptocurrency is VERY risky. Make sure you understand these risks and that you are responsible for what you do with your money.
🔥 If you’re a beginner. I believe the article below will be useful to you ☞ What You Should Know Before Investing in Cryptocurrency - For Beginner
I hope this post will help you.
